The motto “Never have so many people known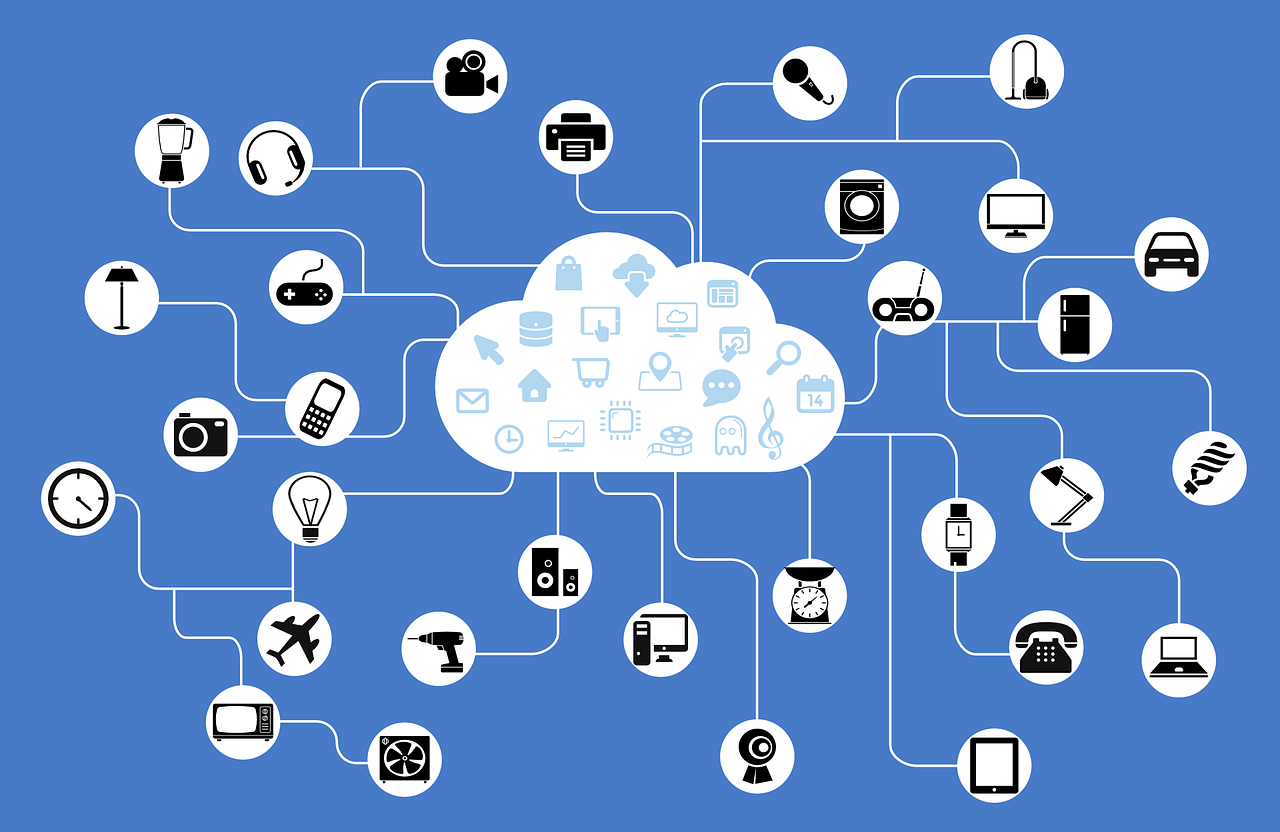 so little about so much,” became a hallmark of James Burke’s brilliant BBC TV Series “Connections” back in the 80’s and 90’s.
so little about so much,” became a hallmark of James Burke’s brilliant BBC TV Series “Connections” back in the 80’s and 90’s.
To paraphrase Burke in terms of the IoT revolution, never will have so many people entrust so much to companies about whose security practices they know so little.
With October serving as Cyber Security Awareness Month, this blog is dedicated to this week’s theme, which touches on IoT, now and in the future.
So what is the Internet of Things anyway?
As defined in Gemalto’s IoT Guidebook, the Internet of Things (IoT) describes an era in which uniquely identifiable devices are able to communicate within the existing Internet infrastructure—providing greater insight and control over elements in our increasingly connected lives. With an estimated 50 billion connected devices estimated to be deployed across the globe by 2020, a pervasive reality of the internet of things is quickly approaching.
This list provides enlightening examples of top IoT sensor-based applications across verticals.
While IoT is quickly presenting vast lifestyle, health and business opportunities, it is also opening a veritable Pandora’s box of yet-to-be addressed security risks. And when it comes to the world of IoT, concerns like privacy and integrity make way for an even great risk—that of personal safety. Security researchers have already demonstrated their ability to hack a car and remotely manipulate its braking system, as well as the eerie prospect of overtaking intravenous devices and altering dosages of medicine delivered to patients.
So what issues do we have to contend with to make IoT safe? Below are just a few.
Establishing security crash tests
In the same way that we rely on standardized crash tests to verify the safety of a car, international standards bodies will have to establish universal security ‘crash tests’ that can reliably establish that a given product is secure and safe to use. A short glance at the breach headlines reflects a reality of security standards that vary widely across verticals and countries, with some sectors lagging a decade or more behind in terms of the countermeasures they use. And with manufacturers producing their IoT wares in one country, selling it in a different country and operating their backend systems in yet another, internationally-recognized standards will become crucial.
Linking smart devices to identities
Browsers are called ‘user agents’ as they perform actions on our behalf. Similarly, connected devices also act on our behalf, yet they may do so independently. We trust connected devices to act on our behalf when giving these devices our credentials (a fingerprint or PIN or digital certificate), or when authorizing them to act on our behalf autonomously. How can we ensure that our trust is not abused by a malicious attacker or malware that has taken over the device. In other words, how will trust be built into the IoT framework to keep us physically safe while using everyday devices such as cars, healthcare devices and doors?
Aggregating control of multiple smart devices
With estimates on the number of things that can be connected in a home reaching the several hundreds, we probably won’t want an app to control each of those things. Instead, we might opt to use service providers that will aggregate all those connected things for us under a single console, to make them manageable once more. And not only will connected homes require management capabilities. Rather any venue that large numbers connected devices will need these to aggregate control of connected devices, including monitoring for anomalies and the issuing of software updates. Harking back to the point above, who will verify that our service provider has secured their systems so that the inhabitants of the connected home stay safe? So that smoke detectors, gates, and thermostats aren’t vulnerable to remote hacking and manipulation?
Monetizing the data
Data is worth money, and with our lives increasingly connected, she who owns the data will own the cash cow. For example, who will own the data harvested by our smart fridge? Will the individual product manufacturers own it? The fridge manufacturer? Or perhaps our internet service provider which enables the traffic of data to flow from the fridge to our grocery store’s replenishment gateway? With IoT net profit estimated by Cisco at $14 Trillion by 2022, will the owner of the IoT data also be accountable for the security of our data and the safety of our person?
To learn more about IOT Security, view our webinar Security and The Internet of Things.


