
2016 marks the 25th anniversary of RSA Conference. This year’s conference theme “Connect to Protect” is very appropriate as the RSA Conference continues to bring thousands of cybersecurity professionals together to learn about new approaches to info security, discover the latest technology and interact with top security leaders and pioneers.
With mega breaches such as Anthem, the IRS, and Sony littering the headlines in 2015, it is vital for today’s IT security professionals to stay up to date on security trends and what better way to stay up to date then attending the largest cybersecurity conference in North America.
If you will be at the RSA Conference at the Moscone Center in San Francisco, CA from February 29th – March 4th, make sure to stop by the Gemalto booth, #4108, in North Hall to learn about how we can help your organization Secure the Breach in three steps – encrypting your sensitive data, managing your encryption keys, and regulating access to your data and applications.
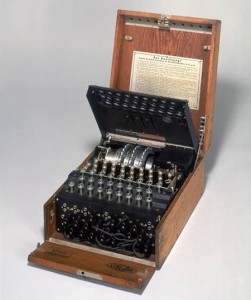 Also at the booth, make sure to see live presentations and demos of our industry leading data protection solutions! Security solutions were not always as cutting edge as they are today. Hear about the evolution of encryption technologies and take a photo with one of the original enigma machines used in the early to mid-twentieth century to protect communications.
Also at the booth, make sure to see live presentations and demos of our industry leading data protection solutions! Security solutions were not always as cutting edge as they are today. Hear about the evolution of encryption technologies and take a photo with one of the original enigma machines used in the early to mid-twentieth century to protect communications.
We’ll also be announcing an RSA Conference photo contest to win prizes including conference t-shirts, phone chargers, and American Express gift cards, so keep your eyes out for a follow-up blog post with all the details.
Rather attend a session? Gemalto’s Vice President of Business Development, David Etue will be presenting on Tuesday, March 1st from 11:10 – 11:40 a.m. in the North Hall briefing center to “Explore the Security of IoT: Trust Comes First”. Make sure you add it your personal agenda.
We hope to see you in San Francisco! Until then, connect with us @GemaltoSecurity on Twitter.


