Home improvement retailer, The Home Depot, 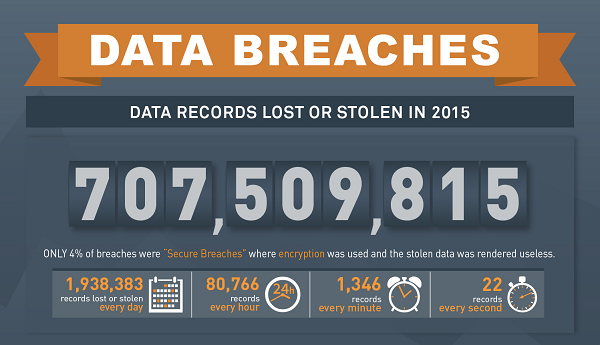 just announced it will pay close to $20 million to compensate its customers affected by a massive 2014 data breach. The company plans to create a $13 million fund to reimburse shoppers for out-of-pocket losses. In addition, at least $6.5 million will be spent to provide cardholders with 1-1/2 years of identity protection services. The retailer said it has already incurred $152 million of pre-tax expenses from the breach, after accounting for expected insurance proceeds.
just announced it will pay close to $20 million to compensate its customers affected by a massive 2014 data breach. The company plans to create a $13 million fund to reimburse shoppers for out-of-pocket losses. In addition, at least $6.5 million will be spent to provide cardholders with 1-1/2 years of identity protection services. The retailer said it has already incurred $152 million of pre-tax expenses from the breach, after accounting for expected insurance proceeds.
Such an expensive outcome to an age old problem—protecting data with a single form of authentication. The Home Depot breach that resulted in the payment card theft of 40 million shoppers, as well as stolen email addresses of 52 to 53 million, was pulled off by hackers who stole the username and password of a single vendor to enter the retailer’s network.
What seems like a basic essential to protecting corporate networks, implementing two-factor authentication, is often ignored. Companies would rather gamble and take the “it won’t happen to us” approach than bet with the odds and realize there is a very good chance that it indeed WILL happen to them. It’s only a matter of time. An intruder who can easily crack the username and password of just one of your users can wreak havoc on your enterprise network. And it may be days, weeks or even months before the intruder is even discovered, giving him/her plenty of time to cause tremendous financial and reputational damage.
So what can your organization learn from The Home Depot’s mistakes? A layered approach is best:
Invest in strong data security: Most importantly, take data breach risks seriously and invest in security. The good news is it appears enterprises are taking that advice. According to findings by 451 Research, nearly half of U.S. enterprises are expected to increase spending in 2016.
Ensure strong identity control: The first line of cyber defense is to protect the perimeters so you know exactly who is accessing specific resources on your network. This is done by implementing security controls that strengthen online identity, including additional factors of identification. By increasing the factors of authentication, you essentially increase the level of security and, as a result, the level of trust given to the identity of the person accessing a computer network or account.
Consider network-based access control: Not everyone in a company should have access to the same types of information. Someone in marketing should not have the same level of access permissions as someone in human resources. With basic network access controls, each user accessing the network has a set of requirements based on job function and access needs.
Invest in data encryption: Encryption for stored information is essential. All data stored on a network server should be encrypted to ensure that even if the data is accessed it is unusable.
As High profile breaches continue to become more frequent and harder to detect and control, organizations around the world are finally waking up and taking a look from the inside out. One fact that seems to be at the center of so many security breaches is traditional password-based authentication.
Check out our Breach Level Index 2015 infographic to quickly review some of the most notable breach statistics of 2015.Want to learn about the data breaches that occurred around the world in 2015? Or, download the complete 2015 Data Breaches Report.


