Over the years, hundreds of customers have made the switch from RSA SecurID to Gemalto’s identity-as-a-service offerings. While RSA was a pioneer in 2FA, Gemalto (formerly SafeNet) became a pioneer in 2FA-as-a-service (see a brief history in this blog.) Why did so many businesses choose Gemalto’s IDaaS solution over the competition?
This blog explores four key reasons:
#1 – A proven technical migration path
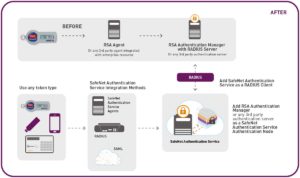
By switching from RSA SecurID to Gemalto, customers don’t need to rip-and-replace anything. Rather, customers can keep their current investment while enjoying fully automated administration and complete visibility from Day 1.
How does it work? Simple. Customers add RSA Authentication Manager (or any other 3rd party RADIUS server) as a client to our IDaaS solution. Each time a user authenticates using RSA SecurID, the event is logged by the IDaaS backend. Customers can automate the migration process by issuing the new Gemalto token only when the RSA SecurID token expires.
To activate their IDaaS account, a user gets a self-enrollment email, through which they also activate their new 2FA authenticator.
#2 –All-inclusive subscription fee
With no hidden fees, Gemalto offers a simple, all-inclusive subscription fee that includes a FREE hardware or software token (which never expire!), customer support and all the latest features and updates. Just subscribe and you’re done.
Want to authenticate with multiple devices? We’ve got you covered with unlimited software tokens per license. And if your business is ‘spiky’ or seasonal in nature, we also offer usage-based billing.
#3 – Lower Total Cost of Operation
Automation is the magic behind Gemalto’s IDaaS offerings. In fact, it is this automation that has won us accolades from partners, customers and analysts alike. Sync your users, set up policies and you’ll never have to manually provision a token again. Your users will be provisioned with the right tokens and permissions as they join the company, leave it or change roles.
Looking to cut access-related helpdesk costs? Our self-service portal allows users to resolve or report numerous issues on their own, helping you lower your support overhead.
And of course, there’s cloud. As a 100% cloud solution, we take care of the security patching, backups, DR/BC and other maintenance aspects, so that you can focus on more strategic projects.
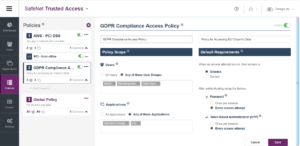
#4 – Cloud compliance
Offering SAML-as-a-service and RADIUS-as-a-service out of the box, Gemalto’s combined access management and MFA solution simplifies cloud compliance with SSO, access policies and authentication—all integrated into one powerful service. By easily setting up policies per compliance mandate, app(s) or group(s), businesses can easily ensure their user access controls are aligned with GDPR, PCI DSS and other regulatory mandates. Policies take just minutes to set up, and allow you to easily add apps, groups and contextual conditions.
“Migration by design” has been at the forefront of Gemalto’s IDaaS solutions – with compatibility and incremental migration built into the service backend. A local UK council and an Irish healthcare system are only a few examples of customers who have eliminated three-year token renewals and high maintenance overheads with the help of fully automated IDaaS delivered from the cloud.
Ready to join them? With Gemalto’s RSA SecurID Buy Back Program, it’s never been more cost effective to make the switch. We are now offering 80% off list price for each active RSA SecurID token in your organization when you migrate to SafeNet Authentication Service or SafeNet Trusted Access.
Claim your 80% off voucher, or learn more by downloading the Four Reasons to Migrate infographic or watching the Best Practices for Migrating from On-Prem to Cloud-based SSO webinar.


