This post originally appeared on SafeNet’s The Art of Data Protection blog prior to SafeNet being acquired by Gemalto.
Medical professionals hailed the technology as “the biggest step towards immortality made in our lifetime.” New devices that would save millions of lives. A new range insulin pumps, defibulators, and implanted devices of all kinds were suddenly prescribed by doctors in every corner of the globe. They promised to provide greater insight into the care of patients, improve the quality of health, and even stop heart attacks as they occurred. And all of this could be done remotely.
The medical professionals were right; these devices did save lives. Unfortunately, they were also been used to destroy them.
In 2031, a patient with an implantable cardioverter defibrillator from the company BioDext dropped dead on stage at a politically rally. Samuel Tuff was the leading candidate for the Bull Moose party and heavily favored to with race for Governor of New York. His heart condition had been well kept from the public, and with his implanted device, his doctors had assured him that he would be fine. When the public learned that he had died of a heart attack, despite having the defibrillator, they demanded to know why the device had failed.
The BioDext device was designed to function at the first sign of significant cardiac arrhythmia, and fire again only if the heart failed to return to normal function. When BioDext investigated, they learned that not only had the defibrillator fired, but it had fired with seemingly no reason for doing so.
Somehow, this device had fired as if it had been commanded by some outside force. It slowly became clear that someone had deliberately hacked Mr. Tuff’s device, and used it to assassinate him in broad daylight.
The assassins revealed themselves hours after the politician’s death. An anarchist group calling themselves “The Pacemakers” claimed responsibility. The Pacemakers were a group of highly skilled hackers who lived and worked in the shadows. Their motives were to realign society in a design more suited to their own ideals, and they had spent years hacking medical devices and stealing medical records in preparation for the events to come. Samuel Tuff, they said, was the first of a long list of targets in all levels of government and enterprise that depended on a medical device they could compromise.
In the following months, more people in positions of power fell victim to the group, as medical device providers like BioDext scrambled to patch security holes in their devices. The devices that once seemed like the future of medicine, were now seen as ticking time-bombs.
 While the story above is an extreme example of what could be possible when hacking implanted medical devices, it illustrates why the security of medical devices must be a top priority.
While the story above is an extreme example of what could be possible when hacking implanted medical devices, it illustrates why the security of medical devices must be a top priority.
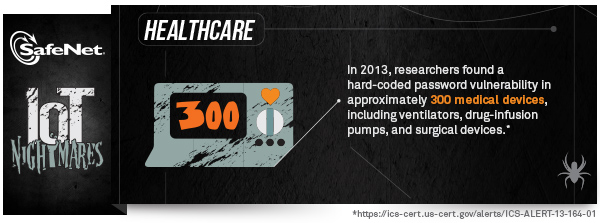
Within healthcare organizations today, a broad assortment of networked medical devices are being employed—and relied upon daily for a range of critical tasks. This can include implanted medical devices that are used to monitor and treat conditions within the individual’s body, such as pacemakers, drug delivery systems, and neuro stimulators. In addition, there are many other networked devices employed within hospitals, including rolling workstations, ventilators, portable ultrasound units, and x-ray machines. Research into the vulnerability of these devices indicated that they are highly vulnerable to compromise.
One of the key challenges in medical device security is the need to prevent unauthorized code from being run on the device. Through code signing, device manufacturers can establish a trusted ecosystem that enables timely, secure delivery of new software and code updates. As a result, device manufacturers can help customers mitigate the exposure associated with unpatched systems and devices.
The IoT Nightmares don’t end here!
Check out the previous entries in the IoT Nightmares blog series:
- Who Turned Out the Lights? – Utilities’ IoT Nightmare
- Prison Break – Correctional Facilities’ IoT Nightmare
- From Riches to Rags – Financial Services’ IoT Nightmare
- Rerouted – Automotive’s IoT Nightmare
- Charge It! – Retail’s IoT Nightmare
You can also play our IoT Nightmares Security Game to explore the risks the Internet of Things introduces to several industries.


