 For years corporations and security professionals have been urged to implement multi-factor authentication (MFA) as the solution for cybersecurity concerns. While MFA isn’t a silver bullet that solves all your cybersecurity concerns, it is a key component in elevating the security of an organization and adding a very important layer of protection. Industry trends are taking MFA to new levels by incorporating it into Access Management Solutions. This shift is being driven by concerns around an evolving IT perimeter where traditional solutions are being exploited and organizations are falling victim to cyber-attacks.
For years corporations and security professionals have been urged to implement multi-factor authentication (MFA) as the solution for cybersecurity concerns. While MFA isn’t a silver bullet that solves all your cybersecurity concerns, it is a key component in elevating the security of an organization and adding a very important layer of protection. Industry trends are taking MFA to new levels by incorporating it into Access Management Solutions. This shift is being driven by concerns around an evolving IT perimeter where traditional solutions are being exploited and organizations are falling victim to cyber-attacks.
The recent news about a breach from Reddit validates the momentum in the cybersecurity world towards access management solutions. The social media platform, considered the 5th top rated website in the U.S., shared that a few of their employees’ administrative accounts were hacked. While they did in fact have their sensitive resources protected with two-factor authentication (2FA), they were surprised to learn that SMS-based authentication was not as secure as they had hoped.
“On June 19, we learned that between June 14 and June 18, an attacker compromised a few of our employees’ accounts with our cloud and source code hosting providers. Already having our primary access points for code and infrastructure behind strong authentication requiring two-factor authentication (2FA), we learned that SMS-based authentication is not nearly as secure as we would hope, and the main attack was via SMS intercept. We point this out to encourage everyone here to move to token-based 2FA.” – Reddit
The weakness in security on the SMS tokens was discussed in 2016 –the draft guideline of the U.S. National Institute for Standards and Technology (NIST) stated that SMS-based two-factor authentication is risky. We also wrote about this in August 2016 in our blog encouraging the use of software tokens which leverage PUSH authentication like the SafeNet MobilePASS+ token.
SAML-based Access Management mitigates risks
Since the issues with SMS have been exposed, why didn’t Reddit implement strong multi-factor using software or hardware based tokens? It turns out they in fact do, as a general practice. In a separate string, Reddit CTO Chris Stowe said that the company, as a rule, had required staff with data access to use a two-factor authentication solution that included a time-based one-time password (TOTP). However, he added, “there are situations where we couldn’t fully enforce this on some of our providers since there are additional “SMS reset” channels that we can’t opt out of via account policy.” Had they protected their resources with a SAML based Access Management Solution this option would be over-ridden immediately mitigating the risk involved with this option. The fact remains that through SMS-based authentication they were exposed –but how did that happen?
Chris Stowe claimed that he knew that the target’s phone wasn’t hacked. However, it is important to understand that the hacking of a phone is only one of the avenues where SMS authentication can be hijacked. We’ve seen examples in movies where a phone is cloned, or when enterprising hackers call the cellphone company to request that the SIM be redirected to a new phone (i.e. call-forwarding).
The intrinsic problem with SMS tokens is that they rely on SS7 or Signaling System Number 7. SS7 is a telephony signaling protocol used by more than 800 telecommunication operators worldwide for information, cross-carrier billing, and enabling roaming, to name a few. There are a number of tools available that can intercept the SS7.
How then did Reddit find themselves exposed? The fact is given enough money and determination, cyber criminals can find ways around many of the safeguards that are put in place today. The most likely scenario is that the hacked users fell victim to phishing or various other social engineering attacks.
Taking Identity and Access Management Solutions to New Levels
These forms of attacks are ultimately what is prompting many security professionals to take their digital security practices to new levels, combining technologies to implement zero trust networks. The importance of implementing a strong authentication solution provided by a trusted vendor cannot be overestimated, organizations simply cannot rely on the use of static passwords any longer.
While Reddit bemoans posthumously that SMS based authentication wasn’t as strong as they thought, this is not the only lesson that can be learned from their exposure. What they were truly lacking was a complete solution which not only enforced multi-factor authentication but also enabled access management controls to be implemented.
Effective Identity Management Integration
Consider for a moment that Reddit had implemented an access management solution alongside their use of 2FA (even with the SMS tokens). A strong access management solution would enable them to create policies around their applications and groups of users, which would have enabled them to continue using their choice 2FA method, but would have added an additional layer of security in the form of context-based authentication, which could have prevented this breach from occurring.
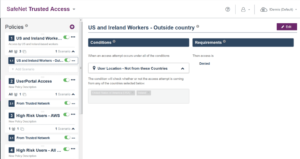
Some examples of beneficial policies for an access management solution would be to consider Reddit’s primary offices being located in the US and Ireland, they could have set up an access policy that would deny access from any country outside of those locations. Or they could set a policy for the group of administrative users who found the use of the multi-factor token cumbersome to leverage their Kerberos ticket when they were in the office and only prompt for OTP when they are working remotely, thus balancing user experience and security and protecting their environment from outsider attacks.
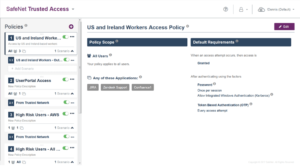
By integrating their systems with an access management solution that supports multiple different authentication methods they could still use the preferred SMS authentication option, but add an access policy which requires them to provide a new unique OTP any time a resource is accessed, or requires the user to input both an OTP as well as their password for an extra layer of authentication security.
Identity Access Management solutions: Access controls adds protection
With a strong access management solution, they would also have access to logs and reporting. This would enable them to isolate and track exactly which users were accessing applications at a given time. If the users were leveraging a software token like MobilePASS+, they would have received a notification when an access attempt was being made by their userID and subsequently had the opportunity to deny the attempt or report it immediately to their security desk.
The problem in this case wasn’t that they were using a weak authentication method, though that certainly didn’t help: The real issue was that the organization was lacking the appropriate access controls — with effective Cloud Access Management, including multifactor authentication, organizations can sufficiently protect their employee’s user identities, their applications containing sensitive data, and prevent customers’ data from being exposed.
Want to prevent breaches and strengthen your Access Management strategy? Read about SafeNet Trusted Access here or Join a 30-minute live demo webinar.
Contibutions in this article from: Ronni Kives


